Every year on March 14th (3.14) people celebrate Pi Day — a day dedicated to the famous mathematical constant and, of course, actual pie. Bakeries run specials, math teachers bring dessert to class, and the internet fills with pie-themed jokes.
But while the world is talking about slices of pie, cybersecurity professionals are looking at a different kind of pie chart.
In cybersecurity, pie charts often tell an important story: how attackers are actually breaking into organizations. And when you look at the data from major 2025 breach reports, one thing becomes clear — a few slices of the “cyberattack pie” account for the majority of real-world incidents.
Recent industry threat reports show that just a handful of attack types dominate the landscape. Understanding these threats can help small businesses, churches, nonprofits, and individuals focus their defenses where they matter most.
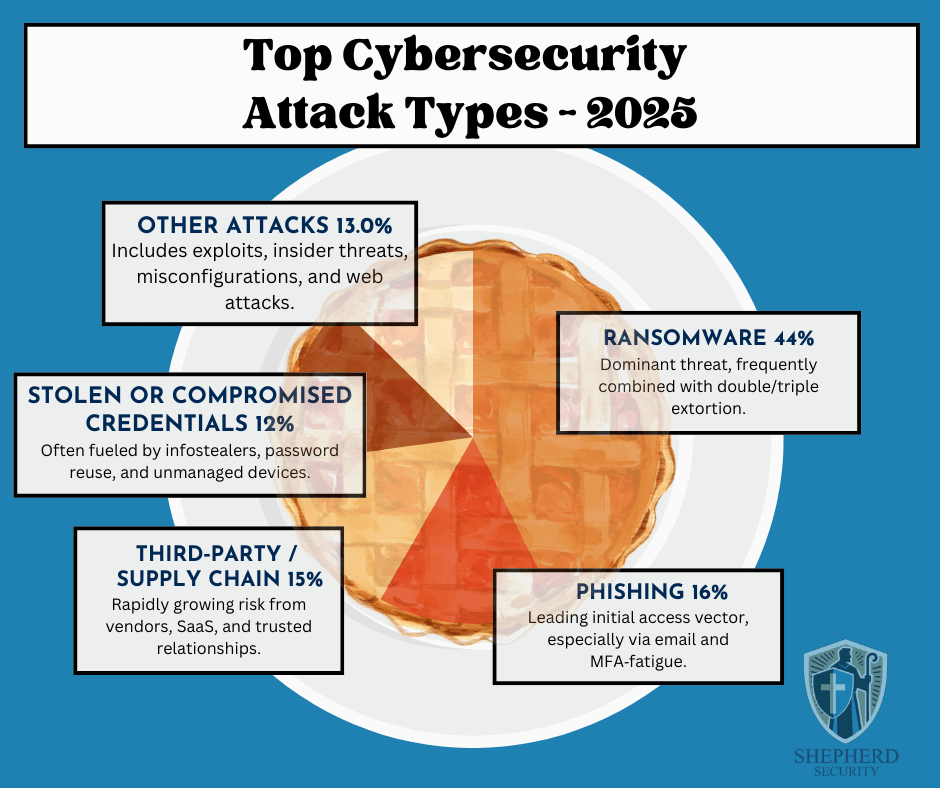
Here’s how the cybersecurity “attack pie” breaks down for 2025:
- Ransomware — 44%
- Phishing — 16%
- Third-Party / Supply Chain Attacks — 15%
- Stolen or Compromised Credentials — 12%
- Other Attacks — 13%
These figures come from a synthesis of multiple industry reports, including the IBM Cost of a Data Breach Report, Verizon’s Data Breach Investigations Report (DBIR), Mandiant M-Trends, and other threat-intelligence research.
For small businesses, churches, nonprofits, and individuals, understanding these threats is one of the most effective ways to prevent becoming the next victim.
1. Ransomware (44%) — The Dominant Cyber Threat
Ransomware continues to dominate the cybercrime landscape.
In a ransomware attack, criminals gain access to a system, encrypt files, and demand payment—often in cryptocurrency—to restore access.
What has changed in recent years is how attackers apply pressure.
Modern ransomware often uses double or even triple extortion, which means attackers will:
• Encrypt your files
• Steal sensitive data
• Threaten to publicly leak the information
For churches, nonprofits, and small organizations, the damage isn’t just operational—it can also destroy trust within a community.
Common entry points include:
- Phishing emails
- Weak or reused passwords
- Unpatched software
- Compromised remote access systems
The takeaway: ransomware rarely starts with sophisticated hacking—it usually starts with someone clicking the wrong thing.
2. Phishing (16%) — The Front Door for Attackers
Phishing remains the single most common way attackers initially gain access to an organization.
A phishing attack is designed to trick someone into believing a message is legitimate. It may look like it comes from:
- A bank
- Microsoft or Google
- A coworker
- A pastor or ministry leader
- A shipping company
The goal is simple: get you to click a link, open an attachment, or enter your login credentials.
In 2025, phishing has become even more dangerous because attackers are using AI tools to craft emails that:
- Contain fewer spelling mistakes
- Sound more natural
- Mimic real organizations convincingly
For many organizations, phishing is the first domino that leads to ransomware or credential theft.
3. Third-Party & Supply Chain Attacks (15%) — Trust Being Exploited
One of the fastest-growing cybersecurity risks involves trusted vendors and services.
Modern organizations rely on dozens of third-party tools:
- Cloud platforms
- Payroll systems
- Donation platforms
- IT providers
- Software vendors
Attackers increasingly target these providers because compromising one trusted partner can give them access to hundreds or thousands of organizations.
If a vendor account is compromised, attackers may:
- Send malicious emails from legitimate systems
- Push malicious updates
- Access sensitive customer or donor information
This is why vendor security and access control are becoming critical parts of cybersecurity programs.
4. Stolen or Compromised Credentials (12%)
Many cyberattacks don’t involve hacking at all.
Instead, attackers simply log in using stolen usernames and passwords.
Credentials are commonly stolen through:
- Phishing emails
- Malware known as infostealers
- Password reuse across multiple websites
- Breached databases sold on dark-web marketplaces
If someone uses the same password for multiple accounts, attackers can use a technique called credential stuffing—trying that password across dozens of systems until something works.
This is why strong password practices and multi-factor authentication (MFA) are essential.
5. Other Attacks (13%)
The remaining category includes a variety of threats such as:
- Software vulnerabilities and exploits
- Insider threats
- Misconfigured cloud services
- Website attacks
- Business email compromise
While these attacks make up a smaller percentage individually, they still represent significant risk—especially for organizations without dedicated IT or security staff.
What This Means for Churches, Small Businesses, and Nonprofits
The key lesson from these statistics is simple:
Most cyberattacks succeed because of human trust and simple mistakes—not technical failures.
That means many attacks can be prevented through basic security practices.
Practical steps every organization should take include:
1. Train staff to recognize phishing
Teach employees and volunteers to slow down, verify unexpected messages, and avoid clicking suspicious links.
2. Require multi-factor authentication (MFA)
This is one of the most effective defenses against credential theft.
3. Use strong, unique passwords
A password manager can make this much easier.
4. Keep systems updated
Patch operating systems and software regularly.
5. Maintain offline or secure backups
Backups are the best defense against ransomware recovery scenarios.
6. Limit vendor and account access
Only grant the minimum access necessary for systems and vendors.
The Bottom Line
Cybersecurity headlines often focus on advanced hacking groups and sophisticated attacks.
But the truth is much simpler.
The majority of breaches come down to four things:
- Someone clicked a phishing email
- Someone reused a password
- A trusted vendor was compromised
- Ransomware followed the initial access
Understanding these patterns allows organizations to focus their defenses where they matter most.
For churches, small businesses, nonprofits, and individuals, cybersecurity doesn’t have to be overwhelming.
Sometimes the most powerful protection is simply awareness, caution, and good security habits.
IBM Security. (2025). Cost of a data breach report 2025.
https://www.ibm.com/security/data-breach
Verizon. (2025). Data breach investigations report (DBIR).
https://www.verizon.com/business/resources/reports/dbir/
Google Cloud Mandiant. (2025). M‑Trends 2025: Cybersecurity insights.
https://www.mandiant.com/resources/m-trends
KnowBe4. (2025). Phishing threat trends report.

Leave a comment